Als Anbieter einer Plattform für integriertes Drohnenmanagement spielt die Sicherheit von Daten, ihrer Übertragung und Verarbeitung eine zentrale Rolle. Im Rahmen der IT- und Datensicherheit stellen sich für FlyNex immer folgende Fragen:
- Wer soll Zugriff auf welche Daten erhalten?
- Welche regulatorischen Vorgaben finden Anwendung?
- Wie lässt sich Datensicherheit und Datenschutz gewährleisten, ohne dass der Mehrwert verloren geht?
In diesem Blog-Artikel gehen wir auf diese Fragen ein und betrachten die Besonderheiten, die Datenerhebungen durch Drohnen mit sich bringen.
Die richtigen Daten zur richtigen Zeit
Gerade in Bezug auf eine (kartenbasierte) Projektverwaltung ist es wichtig, dass Informationen über Objekte oder Projekte einfach abrufbar und aktuell sind. Die Qualität von erfassten Daten setzt sich aus unterschiedlichen Aspekten zusammen:
- Wird die richtige Art von Daten erfasst? Bspw. ist es bei einer Inspektion von Bauwerken erforderlich Bildmaterial in einer hohen Auflösung zu haben. Die Bild-Sensorik (Kamera) ist also ein wichtiges Element.
- Sind Daten vergleichbar? Zum Beispiel, indem Bilder stets aus der selben Position vom gleichen Objekt erfasst werden?
- Sind die Daten verwertbar? Dieser Aspekt wird vor allem in der Nachbetrachtung entscheidend. Stark vereinfacht: Möchte man ein Bild auswerten hilft es wenig, wenn die Daten nur in Text-Format vorliegen.
Ist die Güte der Datenerhebung sichergestellt, ergeben sich häufig Fragen hinsichtlich eines einfachen Rollen- und Rechte-Managements. Es müssen nicht nur die richtigen Daten zur richtigen Zeit erfasst werden und nutzbar sein. Darüber hinaus muss auch klar geregelt werden, wer Zugriff auf welche Informationen erhält und wie dieser Zugriff ausgestaltet ist. Dies beinhaltet nicht nur Zugriffsberechtigte, sondern auch Drittanbieter-Lösungen, technische Infrastruktur und Datenverarbeiter.
IT-Infrastruktur: Auf die Details kommt es an
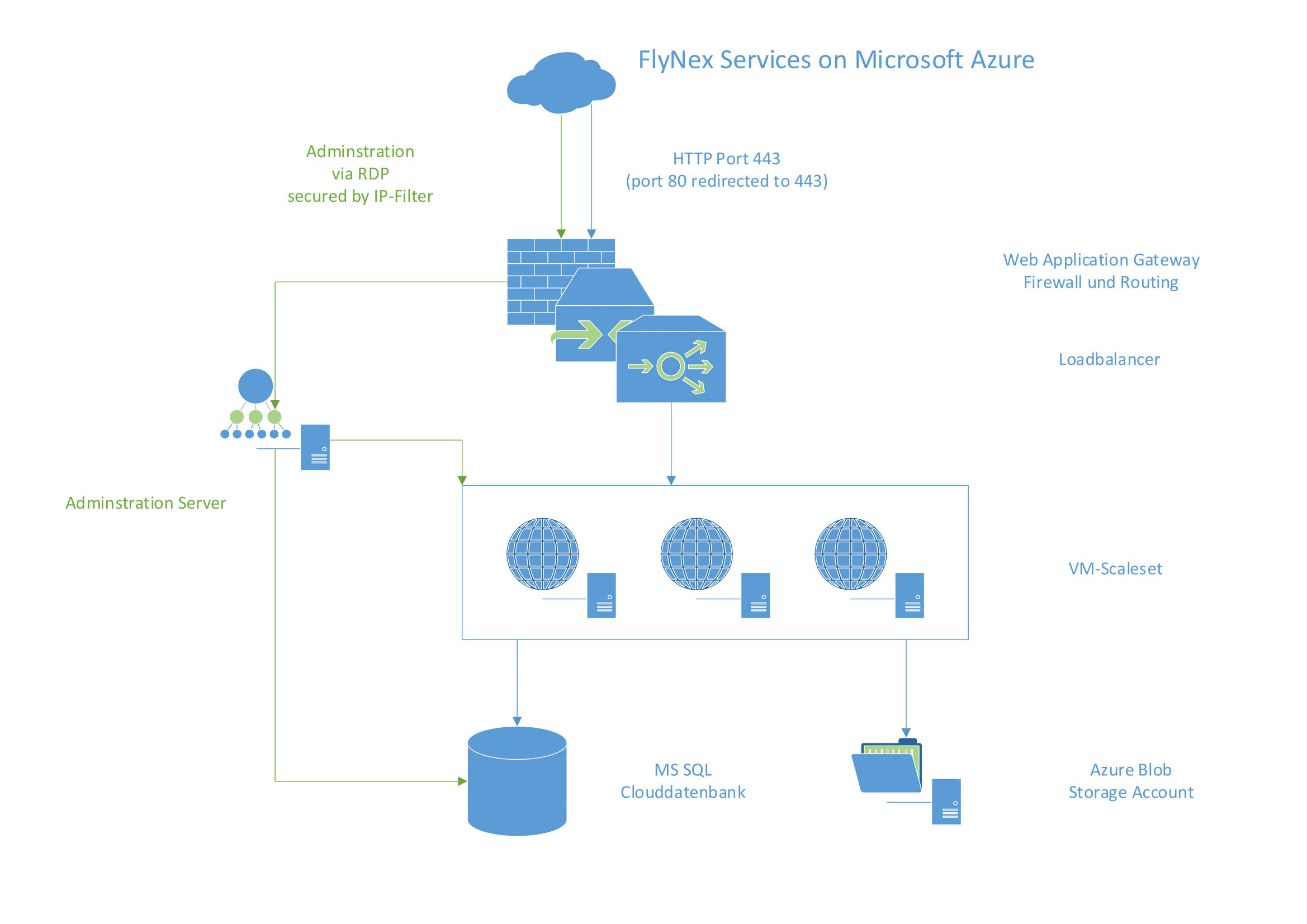
Alle FlyNex-Anwendungen basieren auf dem FlyNex-eigenen IT-Grundschutz, welcher sich stark an den Empfehlungen des Bundesamtes für Sicherheit in der Informationstechnik (BSI) orientiert. Denn in der technischen Betrachtung (siehe Infrastruktur-Schema) muss jede Instanz, die Daten verarbeitet oder speichert, im Kontext der Zugriffs- und Rechteverwaltung überprüft werden. Dies bezieht sich sowohl auf generierte Daten, die mittels Drohnen erfasst wurden, wie auch die Informationen zu Projekten, Mitarbeiter, Planungen u. w., die vom Nutzer selbst eingestellt wurden.
FlyNex betreibt seine Web-Anwendungen aus diesen Überlegungen heraus in einer Microsoft Azure Umgebung. Microsoft erfüllt mit seiner Cloud-Lösung Azure die Bedingungen, um die gesamte Daten-Wertschöpfung stets sicher und performant zu gewährleisten. Aus den FlyNex-IT-Grundschutz-Anforderungen, der Umsetzung des Datenschutzes und dem Sicherheitsbedürfnis resultiert die verwendete FlyNex Cloud-Infrastructure, wie hier dargestellt:
Die Rechenzentren von Microsoft Azure werden geographisch getrennt voneinander betrieben und erfüllen die Standards nach ISO/IEC 27001:2013 und NIST SP 800-53 hinsichtlich Sicherheit und Zuverlässigkeit. Microsoft hat bezüglich des Datenschutzes und Datenzugriffs für Azure DSGVO-konforme Lösungen geschaffen, um die IT-Infrastruktur im Rahmen der EU-weiten und nationalen datenschutzrechtlichen Vorgaben bereitstellen zu können. Somit lässt sich eine 100-prozentige DSGVO-Compliance gewährleisten, gleichzeitig die Datenbereitstellung und -verarbeitung nach EU-Vorgaben gewährleisten.
Verschlüsselung & Zugangskontrolle
Die gesamte Kommunikation der FlyNex-Services erfolgt über das HTTPS-Protokoll und wird asymmetrisch verschlüsselt übermittelt.
In der FlyNex-Infrastruktur selbst sind alle Rechensysteme nur über eigene Gateways erreichbar. Alle Datenzugriffe in der FlyNex-Cloud werden durch ein Monitoring überwacht, um auffällige Zugriffsversuche zu erkennen. Für das Zugriffsmanagement und die Zugriffsprüfung wird ein FlyNex-eigener Authentifizierungsservice betrieben.
Der Zugriff von FlyNex-Diensten und Mitarbeitern innerhalb der Infrastruktur in Deutschland findet über Remote Desktop Protocol (RDP) mit IP-Filter statt und erfordert gesonderte Sicherheitsfreigaben. Dazu nutzen wir die entsprechenden Authentifizierungsmethoden, wie sie gemäß Sicherheitsstandards empfohlen sind und von Azure bereitgestellt werden.
Zusammengefasst: Alle geforderten Sicherheitsaspekte werden durch Azure umgesetzt und FlyNex hat gemäß der deutschen (BDSG) und europäischen (DSGVO) Datenschutzrichtlinien die Kontrolle über die Daten der Nutzer, die mittels eines Datentreuhänders auch gegenüber Dritten gewährleistet sind. FlyNex hat die Azure-Umgebung gemäß den Richtlinien des IT-Grundschutzes aufgesetzt und betreibt diese entsprechend, um maximale Sicherheit zu erreichen und Datenschutz zu gewährleisten.
Zugriffsmanagement und Rechteverwaltung innerhalb der Anwendungen
Auf Nutzerebene lassen sich verschiedene Zugriffsrechte vergeben und verwalten. In der Map2Fly Pro und FlyNex Enterprise Suite wurde dazu ein ausgereiftes Rollen- und Rechtemanagement implementiert. Somit lässt sich festlegen, welcher Nutzer in einem Projekt auf welche hinterlegten Daten und Informationen Zugriff hat und sie ggf. auch bearbeiten kann. Vereinfacht dargestellt gibt es zwei Ebenen: die Berechtigungsebene und die Projektebene.
Auf der Berechtigungsebene sind die Administratoren und Benutzer zu finden. Die Rolle „Benutzer“ ist die Standardrolle für neu erstellte Nutzer.
Hinweis: Die Berechtigungsrolle Benutzer ist unabhängig von der eigentlichen Benutzerlizenz.
In der Projektebene lassen sich die Rechte der Projektteilnehmer managen.
Welche Rollen können zugeteilt werden?
Vom Piloten in die Cloud: Datenübertragung schützen

Neben unseren bekannten Anwendungen Map2Fly und der FlyNex Corporate Platform, haben wir die Connect App als Ergänzung entwickelt. Die Connect App ist die Schnittstelle zwischen Fluggerät und unserer Planungssoftware.
Da es sich um eine Android App handelt, kann sie auf unterstützten Android-basierten Controllern oder mobilen Endgeräten installiert werden. Die App verbindet sich mit dem genutzten Gerät und bildet eine Relais-Station zwischen Drohnen-Daten und anderen Endpunkten. Die generierten Daten werden von dem Gerät mit der Connect App, über eine verschlüsselte mobile Verbindung (HTTPS) auf die FlyNex Corporate Platform übermittelt. Hierzu betreibt FlyNex entsprechende API’s, also Schnittstellen zwischen Controllern und Plattform-Infrastruktur, um eintreffende Datenverbindungen zu authentifizieren und zu entschlüsseln.
 Michael Petrosjan CFO & Co-Founder, FlyNex GmbH |
REGELN UND LEITLINIEN – WIE SETZT MAN RECHTSSICHER DROHNEN EIN, OHNE SICH EINZUSCHRÄNKEN?Was im ersten Augenblick wirkt, als ob es sich gegenseitig ausschließt, lässt sich in genauerer Betrachtung recht gut miteinander vereinen. Regulatorische Rahmen für Drohnen-Anwendungen und operative Anforderungen fürs eigene Unternehmen, bzw. für eigene Projekte, sind in der Planungsphase entscheidende Einflussfaktoren. Unser Fokus dabei ist es, eine effiziente Planung für komplexe Datenerhebungen in automatisierte Prozesse zu übertragen. Sie haben Fragen zu unserer Lösung oder zu bestimmten Anwendungsfällen? Schreiben Sie uns einfach oder rufen Sie an. |